Overview: A Roadmap for the National Cybersecurity Strategy
The White House released its implementation plan for the National Cybersecurity Strategy (the Strategy) unveiled in March 2023. The plan provides a roadmap outlining how the Nation will achieve the President’s vision for cyber resilience in America.
Overall, the primary purpose of the publication is to pave the path for achieving two significant shifts: more capable actors in cyberspace to bear more of the responsibility for cybersecurity and increased incentives to make investments in long-term resilience. In other words, it serves to help secure cyberspace and ensure that the United States can fully benefit from its digital future.
As the first iteration of the Implementation Plan, it’s a living document meant to be updated in concert with the evolving cyber landscape.
The National Cybersecurity Strategy
The Strategy, consisting of five pillars and 27 strategic objectives, addresses the importance of cybersecurity and how it impacts various aspects of American life, such as the economy, critical infrastructure, democracy, privacy, and national defense. Additionally, it emphasizes the need for collaboration between the public and private sectors to achieve effective and equitable cybersecurity. It also aims to shift responsibility from individual users and small organizations to encourage long-term investments in security and resilience.
What are the Main Components of the Implementation Plan?
In alignment with the Strategy, the 57-page Implementation Plan comprises details for the Strategy’s five key pillars and related strategic objectives and sub-initiatives. All of which provide a means to achieve a wide range of goals for the future of cybersecurity in America. The plan comes with more than 65 initiatives assigned to 18 federal agencies with timelines for completion.
Pillar One: Defend Critical Infrastructure
To begin, Pillar One consists of five strategic objectives, including 16 sub-initiatives. Overall, it focuses on the universal implementation of baseline configurations, the development of Incident Response Plans and Processes, and the implementation of federal cybersecurity centers.
Strategic Objective 1.1: Establish Cybersecurity Requirements to Support National Security and Public Safety
- Strategic Initiative 1.1.1: Establish an initiative on cyber regulatory harmonization
- Strategic Initiative 1.1.2: Set cybersecurity requirements across critical infrastructure sectors
- Strategic Initiative 1.1.3: Increase agency use of frameworks and international standards to inform regulatory alignment
Strategic Objective 1.2: Scale Public-Private Collaboration
- Strategic Initiative 1.2.1: Scale public-private partnerships to drive development and adoption of secure-by-design and secure-by-default technology
- Strategic Initiative 1.2.2: Provide recommendations for the designation of critical infrastructure sectors and SRMAs
- Strategic Initiative 1.2.3: Evaluate how CISA can leverage existing reporting mechanisms or the potential creation of a single portal to integrate and operationalize SRMAs’ sector-specific systems and processes
- Strategic Initiative 1.2.4: Investigate opportunities for new and improved information-sharing and collaboration platforms, processes, and mechanisms.
- Strategic Initiative 1.2.5: Establish an SRMA support capability
Strategic Objective 1.3: Integrate Federal Cybersecurity Centers
- Strategic Initiative 1.3.1: Assess and improve Federal Cybersecurity Centers’ and related cyber centers’ capabilities and plans necessary for collaboration at speed and scale.
Strategic Objective 1.4: Update Federal Incident Response Plans and Processes
- Strategic Initiative 1.4.1: Update the National Cyber Incident Response Plan (NCIRP)
- Strategic Initiative 1.4.2: Issue final Cyber Incident Reporting for Critical Infrastructure Act (CIRCIA) rule
- Strategic Initiative 1.4.3: Develop exercise scenarios to improve cyber incident response
- Strategic Initiative 1.4.4: Draft legislation to codify the Cyber Safety Review Board (CSRB) with the required authorities
Strategic Objective 1.5: Modernize Federal Defenses
- Strategic Initiative 1.5.1: Secure unclassified Federal Civilian Executive Branch (FCEB) systems
- Strategic Initiative 1.5.2: Modernize Federal Civilian Executive Branch (FCEB) technology
- Strategic Initiative 1.5.3: Secure National Security Systems (NSS) at Federal Civilian Executive Branch (FCEB) agencies
Pillar Two: Disrupt and Dismantle Threat Actors
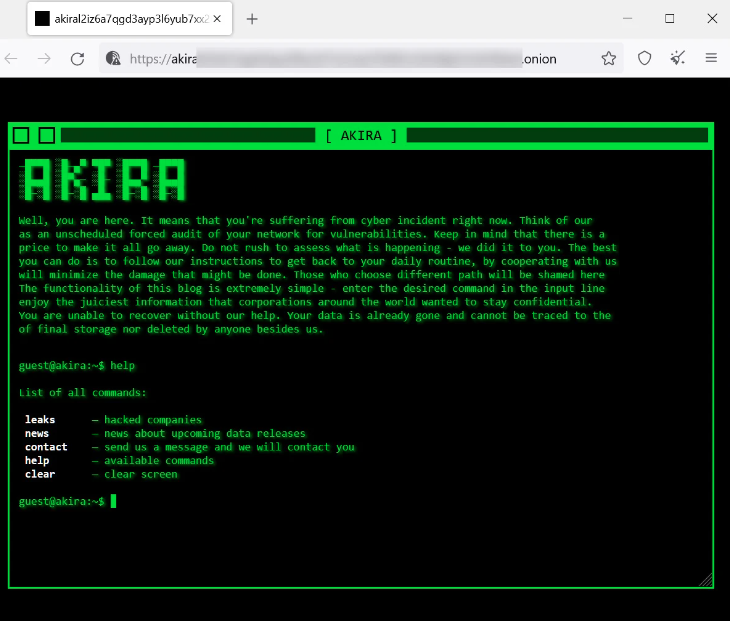
Next, Pillar Two consists of five strategic objectives and 14 strategic sub-initiatives. In all, this pillar aims to strengthen the National Cyber Investigative Joint Task Force’s capacity and expand other organizations that may coincide. Furthermore, it acknowledges that with increased power comes the responsibility to take down threat actors and support organizations that fall victim to ransomware or other cybercrimes.
Strategic Objective 2.1: Integrate Federal Disruption Activities
- Strategic Initiative 2.1.1: Publish an updated DOD Cyber Strategy
- Strategic Initiative 2.1.2: Strengthen the National Cyber Investigative Joint Task Force (NCIJTF) capacity
- Strategic Initiative 2.1.3: Expand organizational platforms dedicated to disruption campaigns
- Strategic Initiative 2.1.4: Propose legislation to disrupt and deter cybercrime and cyber-enabled crime
- Strategic Initiative 2.1.5: Increase speed and scale of disruption operations
Strategic Objective 2.2: Enhance Public-Private Operational Collaboration to Disrupt Adversaries
- Strategic Initiative 2.2.1: Identify mechanisms for increased adversarial disruption through public-private operational collaboration
Strategic Objective 2.3: Increase the Speed and Scale of Intelligence Sharing and Victim Notifications
- Strategic Initiative 2.3.1: Identify and operationalize sector-specific intelligence needs and priorities.
- Strategic Initiative 2.3.2: Remove barriers to delivering cyber threat intelligence and data to critical infrastructure owners and operators
Strategic Objective 2.4: Prevent Abuse of U.S.-Based Infrastructure
- Strategic Initiative 2.4.1: Publish a Notice of Proposed Rulemaking on requirements, standards, and procedures for Infrastructure-as-a-Service (IaaS) providers and resellers
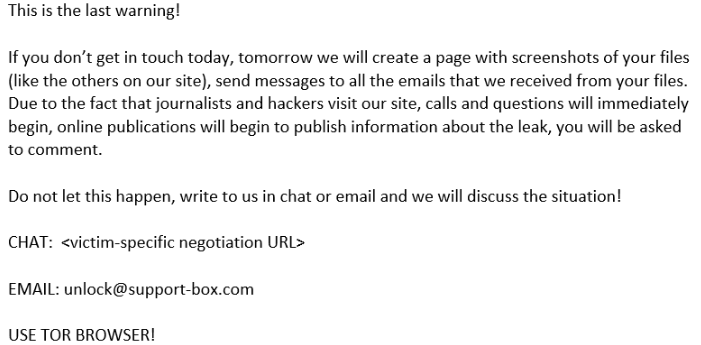
Strategic Objective 2.5: Counter Cybercrime, Defeat Ransomware
- Strategic Initiative 2.5.1: Disincentivize safe havens for ransomware criminals
- Strategic Initiative 2.5.2: Disrupt ransomware crimes
- Strategic Initiative 2.5.3: Investigate ransomware crimes and disrupt the ransomware ecosystem.
- Strategic Initiative 2.5.4: Support Private sector and state, local, Tribal, and territorial (SLTT) efforts to mitigate ransomware risk.
- Strategic Initiative 2.5.5: Support other countries’ efforts to adopt and implement the global anti-money laundering/countering the financing of terrorism (AML/CFT) standards for virtual asset service providers.
Pillar Three: Shape Market Forces to Drive Security and Resilience
Thirdly, Pillar Three comprises five strategic objectives and 11 strategic sub-initiatives. This portion of the plan prioritizes the security of devices and services but also holds accountability for the risk they might present. By using federal grants and other incentives, developers will prioritize security in the first step of a product rather than once it has been released. Additionally, Pillar Three highlights the importance of Cyber Liability Insurance for a catastrophic cyber event.
Strategic Objective 3.2: Drive the Development of Secure IoT Devices
- Strategic Initiative 3.2.1: Implement Federal Acquisition Regulation (FAR) requirements per the Internet of Things (IoT) Cybersecurity Improvement Act of 2020
- Strategic Initiative 3.2.2: Initiate a U.S. Government IoT security labeling program
Strategic Objective 3.3: Shift Liability for Insecure Software Products and Services
- Strategic Initiative 3.3.1: Explore approaches to develop a long-term, flexible, and enduring software liability framework
- Strategic Initiative 3.3.2: Advance software bill of materials (SBOM) and mitigate the risk of unsupported software
- Strategic Initiative 3.3.3: Coordinated vulnerability disclosure
Strategic Objective 3.4: Use Federal Grants and Other Incentives to Build in Security
- Strategic Initiative 3.4.1: Leverage Federal grants to improve infrastructure cybersecurity
- Strategic Initiative 3.4.2: Prioritize funding for cybersecurity research
- Strategic Initiative 3.4.3: Prioritize cybersecurity research, development, and demonstration on social, behavioral, and economic research in cybersecurity
Strategic Objective 3.5: Leverage Federal Procurement to Improve Accountability
- Strategic Initiative 3.5.1: Implement Federal Acquisition Regulation (FAR) changes required under EO 14028
- Strategic Initiative 3.5.2: Leverage the False Claims Act to improve vendor cybersecurity
Strategic Objective 3.6: Explore a Federal Cyber Insurance Backstop
- Strategic Initiative 3.6.1: Assess the need for a federal insurance response to a catastrophic cyber event
Pillar Four: Invest in a Resilient Future
Then, Pillar Four entails five strategic objectives and 13 strategic sub-initiatives. It sets the tone for what the future holds in terms of strategy and security by developing network security best practices and building training, tools, and support for engineers and technicians using cyber-informed engineering principles.
Strategic Objective 4.1: Secure the Technical Foundation of the Internet
- Strategic Initiative 4.1.1: Lead the adoption of network security best practices
- Strategic Initiative 4.1.2: Promote open-source software security and the adoption of memory safe programming languages
- Strategic Initiative 4.1.3: Accelerate the development, standardization, and adoption of foundational Internet infrastructure capabilities and technologies
- Strategic Initiative 4.1.4: Accelerate the development and standardization, and support the adoption, of foundational internet infrastructure capabilities and technologies
- Strategic Initiative 4.1.5: Collaborate with key stakeholders to drive secure Internet routing
Strategic Objective 4.2: Reinvigorate Federal Research and Development for Cybersecurity
- Strategic Initiative 4.2.1: Accelerate maturity, adoption, and security of memory-safe programming languages
Strategic Objective 4.3: Prepare for Our Post-Quantum Future
- Strategic Initiative 4.3.1: Implement National Security Memorandum-10
- Strategic Initiative 4.3.2: Implement NMS-10 for National Security Systems (NSS)
- Strategic Initiative 4.3.3: Standardize, and support the transition to, post-quantum cryptography algorithms.
Strategic Objective 4.4: Secure Our Clean Energy Future
- Strategic Initiative 4.4.1: Drive adoption of cyber secure-by-design principles by incorporating them into Federal projects
- Strategic Initiative 4.4.2: Develop a plan to ensure the digital ecosystem can support and deliver the U.S. Government’s decarbonization goals
- Strategic Initiative 4.4.3: Build and refine training, tools, and support for engineers and technicians using cyber-informed engineering principles
Strategic Objective 4.6: Develop a National Strategy to Strengthen Our Cyber Workforce
- Strategic Initiative 4.6.1: Publish a National Cyber Workforce and Education Strategy and track its implementation
Pillar Five: Forge International Partnerships to Pursue Shared Goals
Finally, Pillar Five includes five strategic objectives with 12 strategic sub-initiatives. Simply put, this pillar promotes collaboration with other countries and allied partners to advance common cybersecurity interests. In effect, these partnerships can establish weaknesses, strengthen the international partner’s cyber capacity, and promote a more diverse and resilient supply chain of trustworthy information and communication vendors.
Strategic Objective 5.1: Build Coalitions to Counter Threats to our Digital Ecosystem
- Strategic Initiative 5.1.1: Create interagency teams for regional cyber collaboration and coordination
- Strategic Initiative 5.1.2: Publish an International Cyberspace and Digital Policy Strategy
- Strategic Initiative 5.1.3: Strengthen Federal law enforcement collaboration mechanisms with allies and partners
- Strategic Initiative 5.1.4: Regional cyber hubs study
Strategic Objective 5.2: Strengthen International Partner Capacity
- Strategic Initiative 5.2.1: Strengthen international partners’ cyber capacity
- Strategic Initiative 5.2.2: Expand international partners’ cyber capacity through operational law enforcement collaboration
Strategic Objective 5.3: Expand U.S. Ability to Assist Allies and Partners
- Strategic Initiative 5.3.1: Establish flexible foreign assistance mechanisms to provide cyber incident response support quickly
Strategic Objective 5.4: Build Coalitions to Reinforce Global Norms of Responsible State Behavior
- Strategic Initiative 5.4.1: Hold irresponsible states accountable when they fail to uphold their commitments
Strategic Objective 5.5: Secure Global Supply Chains for Information, Communications, and Operational Technology Products and Services
- Strategic Initiative 5.5.1: Promote the development of secure and trustworthy information and communication technology (ICT) networks and services
- Strategic Initiative 5.5.2: Promote a more diverse and resilient supply chain of trustworthy information and communication (ICT) vendors
- Strategic Initiative 5.5.3: Begin administering the Public Wireless Supply Chain Innovation Fund (PWSCIF)
- Strategic Initiative 5.5.4: Promulgate and amplify Cybersecurity Supply Chain Risk Management (C-SCRM) key practices across and within critical infrastructure sectors
Implementation-wide Initiatives
Lastly, a sixth component of the plan highlights the effectiveness of reviewing progress and applying lessons learned throughout the implementation of the National Cybersecurity Strategy roadmap.
Implementation 6.1: Assessing Effectiveness
- Initiative 6.1.1: Report progress and effectiveness on implementing the National Cybersecurity Strategy
- Initiative 6.1.2: Apply lessons learned to the National Cybersecurity Strategy implementation
- Initiative 6.1.3: Align budgetary guidance with National Cybersecurity Strategy implementation.
What Does the Implementation Plan Mean for Other Organizations?
The release of the National Cybersecurity Strategy Implementation Plan by the White House has significant implications for commercial businesses, state and local governments, school districts, and other organizations in the United States. This plan outlines the government’s strategy and actions to strengthen the nation’s cybersecurity defenses and protect critical infrastructure from cyber threats.
The release of the National Cybersecurity Strategy Implementation Plan should be of great importance to all organizations because:
- Improved Cybersecurity Defense: The plan outlines strategies to enhance the nation’s cybersecurity capabilities, which will benefit organizations by providing a safer digital environment.
- Regulatory Compliance: Organizations may need to comply with new cybersecurity regulations resulting from the implementation plan, which could impact their operations and reputations.
- Collaborative Approach: Organizations that participate in public-private partnerships may gain access to valuable threat intelligence and resources to bolster their cybersecurity defenses.
- Protection of Critical Infrastructure: The plan’s focus on protecting critical infrastructure helps ensure the continuity of essential services during cyber incidents.
Ultimately, the release of the National Cybersecurity Strategy Implementation Plan reflects the government’s commitment to addressing cyber threats at a national level. In light of this historical development, organizations should closely monitor its impact on their industries and be prepared to adapt their cybersecurity practices to align with the evolving strategies and initiatives set forth by the plan.
To review the National Cybersecurity Strategy Implementation Plan in greater detail, click here.
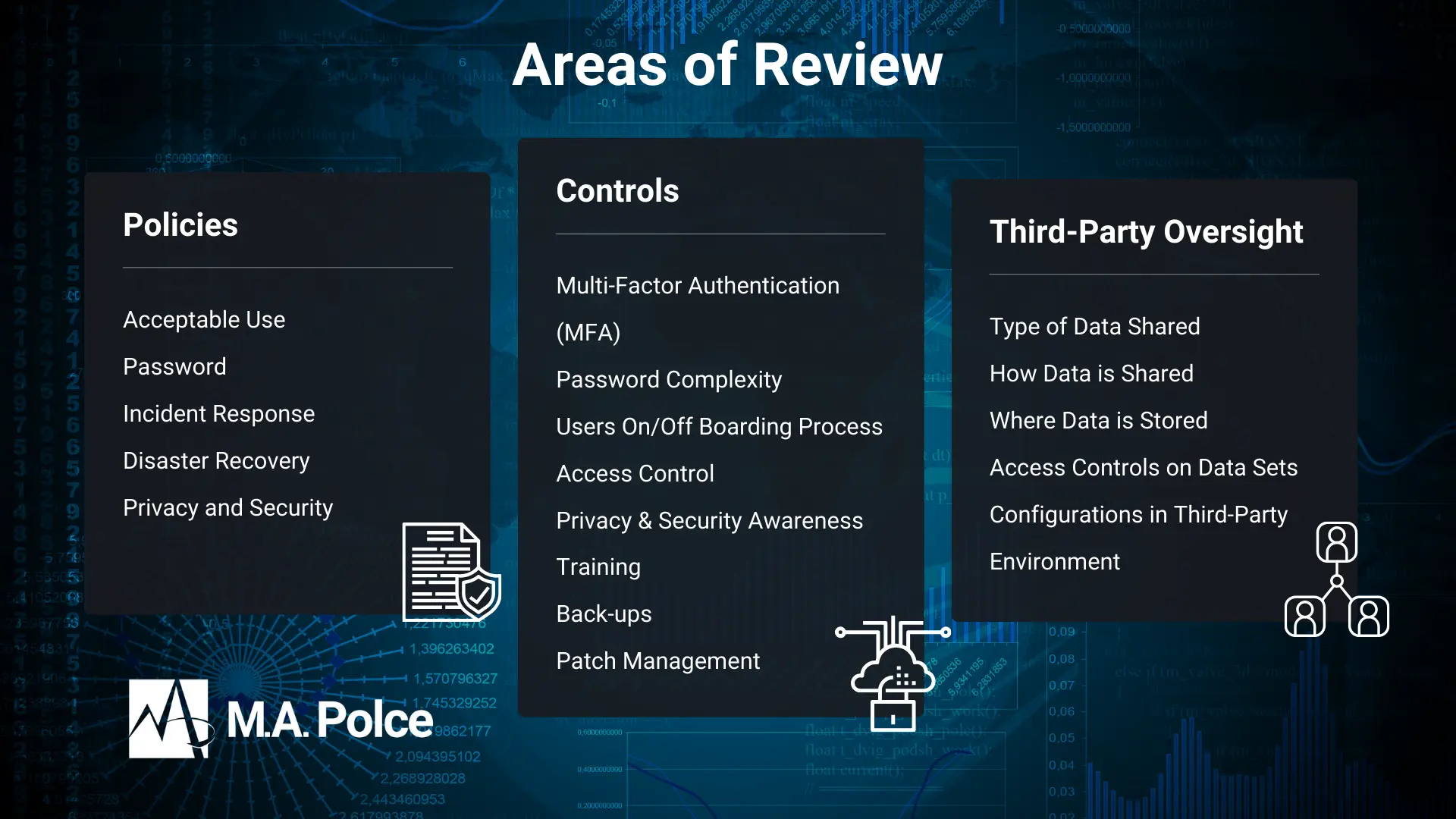
How to Address Cybersecurity at Your Organization
Are you prepared to fortify your organization’s cybersecurity defenses in alignment with the United States’ National Cybersecurity Strategy Implementation Plan? Protect your business from cyber threats and embrace proactive measures to safeguard your digital assets. Contact M.A. Polce today and secure your organization’s future with our expert cybersecurity solutions.
At M.A. Polce, we understand the critical importance of staying ahead of cyber adversaries in this rapidly evolving landscape. Our tailored cybersecurity services are designed to meet the unique needs of businesses like yours. With the White House’s focus on national cybersecurity, it’s the ideal time to ensure your organization is equipped to face any cyber challenge.
Let our team of certified experts assess your current security posture, identify vulnerabilities, and implement robust defenses. By partnering with M.A. Polce, you’ll gain access to industry-leading cybersecurity strategies and cutting-edge technologies to protect your valuable data and maintain your reputation.
Don’t wait for cyber threats to strike. Reach out to M.A. Polce today and join us in building a safer and more resilient digital ecosystem for your organization. Together, we’ll navigate the complexities of cybersecurity and create a stronger, more secure future for your business.