Staying Ahead of the Game in a Constantly Evolving Threat Landscape
Why is threat intelligence so important for your cyber defense strategy? Because businesses can expect cyber threats to become an even more significant concern in the coming years. In fact, some estimates project the global cost of cybercrime to reach $10.5 trillion by 2025. Predictions like this stress the importance of proactive threat hunting backed by threat intelligence.
One step businesses can take to increase the effectiveness of cybersecurity measures is to employ threat intelligence through managed detection and response (MDR). Part of a larger MDR plan, threat intelligence provides organizations with the information they need to protect corporate data from cyber threats. It enables businesses to move from reactive to proactive cybersecurity, helping them save significant time and money with IT security.
Understanding Threat Intelligence
To enhance their MDR approach, businesses gather data from various sources regarding past cyberattacks, potential future incidents, and current concerns. This data is then collected, interpreted, and analyzed to create threat intelligence.
Threat intelligence transforms unorganized, unconnected threat information into actionable data, highlighting the level of cyber risk an organization faces. Additionally, it allows businesses to better understand the tactics cybercriminals use, empowers the development of more effective security controls, and helps prevent advanced cyberattacks.
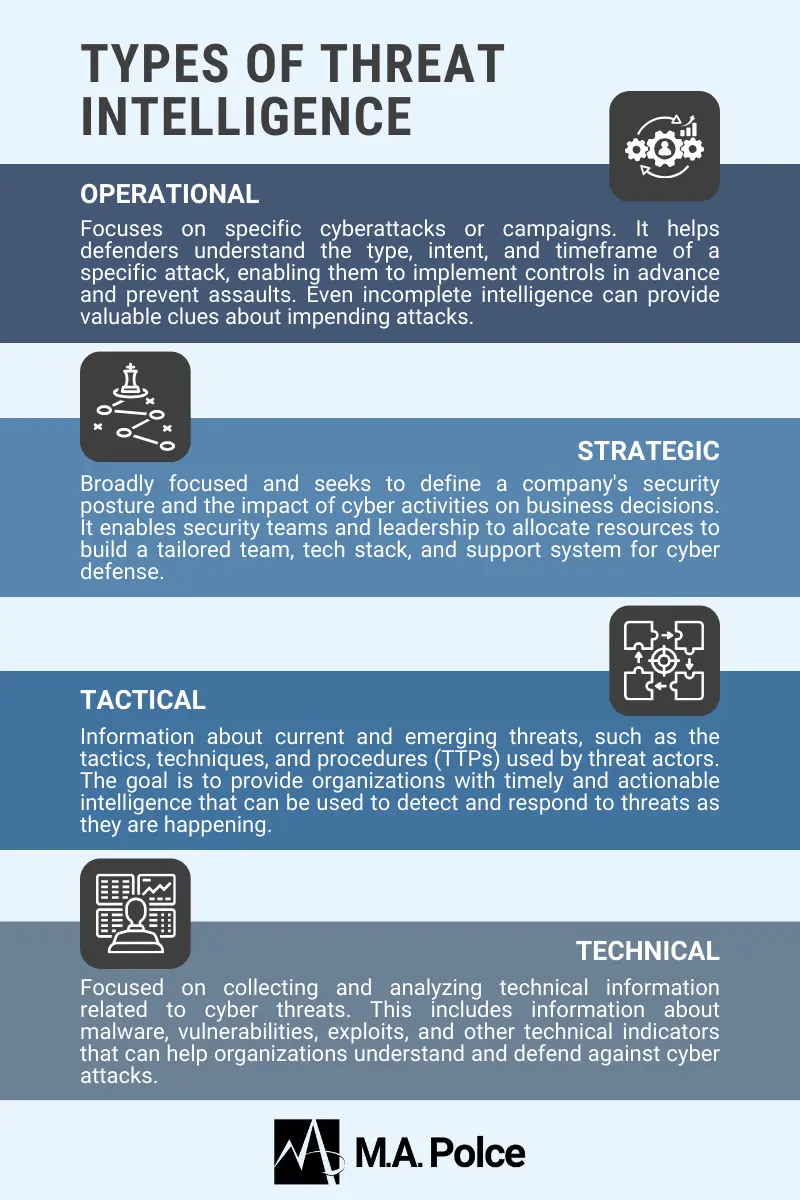
Part of why threat intelligence is necessary is because information about cyber threats comes from numerous sources. This data may include details of attack methods, steps for identifying an attack in progress, and the different ways these attacks affect companies. For this reason, the basis from which you obtain threat information may depend on the type of threat intelligence. These types include:
Operational
Operational threat intelligence helps IT teams take action against a specific attack. It may include information about the timing of the attack and its planned intent. The trouble with operational threat intelligence is that it comes from the cybercriminal, making it hard to obtain.
Strategic
Strategic threat intelligence shows IT departments the context of an attack. For instance, it could include an analysis of an initiative to determine its cybersecurity risk. It’s beneficial when IT directors want to present findings to the board of directors or executive personnel and need to weed out more technical information.
Senior leadership often uses this type of threat intelligence to make strategic decisions about cybersecurity investments and priorities.
Tactical
Tactical threat intelligence focuses on how threat actors carry out attacks, as well as the tools IT teams use to defend against them. It also helps a business evaluate the likelihood of becoming a target for different attacks. Tactical threat intelligence enables better decision-making for security controls and defense strategies. Examples include information about common attack infrastructures, and the tools threat actors use, as well as the types of organizations they target.
Technical
Technical threat intelligence is clear evidence of an attack in progress, sometimes called indicators of compromise (IOCs). This information includes the IP addresses, command-and-control infrastructures (C2 infrastructures), scam emails from phishing, or aspects of malware.
The Role of Threat Intelligence in MDR
Threat intelligence is central to managed detection and response (MDR). This outsourced service helps organizations improve their approach to cybersecurity by targeting advanced threats to eradicate them. It’s especially beneficial for small to medium-sized businesses that may not have the resources to secure an in-house security team.
MDR services comprise a range of technologies and processes to fortify defenses across the entire IT infrastructure. This allows providers to prevent the spread of an attack if one occurs. One such component of MDR that service providers leverage is advanced threat intelligence.
Threat intelligence allows companies to determine which threats are most likely to affect an IT infrastructure based on the specific concerns of the business. Instead of following predefined guidelines to detect known threats like some antivirus solutions do, threat intelligence enables MDR service providers to find and address threats that may go unnoticed.
In other words, MDR providers can use threat intelligence information to create custom rules and alerts and tailor them to the specific threats facing an organization. Unlike traditional antivirus solutions that rely on known signatures, MDR technologies can detect new and emerging threats that may not be recognized by traditional methods.
Because threat intelligence allows MDR to detect ‘hidden’ attacks, it enhances proactive threat hunting. This technique involves searching for previously unknown threats that may go undetected for long periods, giving cybercriminals continued access to sensitive data. Proactive threat hunting provides IT teams with a more accurate picture of the company’s cybersecurity posture and can improve incident response speed.
Recognizing Tradecraft with Threat Intel
Managed Detection and Response (MDR) technologies also leverage threat intelligence to recognize hacker tradecraft. It does this by using a combination of machine learning algorithms and human analysis.
In the context of cybercrime, the term “tradecraft” refers to the techniques and methods used by attackers to penetrate a target system or network. This includes tactics such as social engineering, phishing, malware deployment, and exploitation of vulnerabilities. Tradecraft encompasses the entire process of planning, executing, and covering up a cyberattack and often involves sophisticated and stealthy methods designed to avoid detection. Hackers may spend years developing and refining their tradecraft in order to carry out successful attacks and evade attribution.
Threat intelligence provides information about known and emerging threats, as well as details on the methods and techniques being used by attackers. This information is used to develop rules and algorithms that can identify patterns and behaviors associated with malicious activity.
In this way, threat intelligence is circular. First, threat information is collected and interpreted into valuable threat intelligence for making cybersecurity decisions. Then, it’s continuously reevaluated as new information is gathered. This framework helps enhance detection and response capabilities and eliminate gaps in threat intelligence.
The Benefits of Using Threat Intelligence in MDR
Interest in threat intelligence is growing. According to a report from Fortune Business Insights, the global threat intelligence market value was $4.24 billion in 2022 and is projected to grow to $18.11 billion by 2023. Why? Threat intelligence is an invaluable asset of MDR because it helps businesses achieve the following:
- Improved threat detection and prevention: By identifying known and unknown attacks that can strike anywhere within the IT infrastructure, threat intelligence augments detection and prevention.
- Faster response times to security incidents: Real-time assessments of attacks empower rapid response to minimize the impact of a security event.
- Reduced risk of data breaches and cyber attacks: Threat intelligence supplies teams with insights on different types of attacks, helping them understand how cybercriminals may act in the future to prevent recurrences.
- Cost savings and improved return on investment (ROI): The average cost of a data breach in the United States was $9.44 million in 2022. Reduced instances of cyber attacks mean significant cost savings for businesses, proving MDR services are well worth the investment.
High-Quality MDR Services with Threat Intel from M.A. Polce
As the threat landscape changes, businesses will face more challenges in protecting their systems, networks, and data. Threat intelligence will only become more important in devising cybersecurity strategies that consider entire IT infrastructures. Small and mid-sized businesses that wish to enhance IT security but lack the resources for an internal team can obtain MDR services from M.A. Polce.
As a managed security services provider (MSSP), M.A. Polce offers MDR services that include continuous monitoring of networks and devices to protect companies against the latest cyber threats. For all our IT solutions, we deliver structured support services and offer clients access to state-of-the-art technology. Contact us today to learn more about our MDR and cybersecurity services.
Sources:
Tech Target
VMware
Security Boulevard
IansResearch
Cambridge Dictionary
Cyber Intelligence Tradecraft Report